X.509 is a crucial ITU standard defining the format for public key certificates, vital for secure communication. These certificates are widely used in Internet protocols like TLS/SSL, which underpins HTTPS for secure web browsing. Beyond online applications, X.509 certificates also play a key role in offline uses such as electronic signatures. In essence, X.509 provides a standardized method for verifying the authenticity and integrity of digital identities, securing both online and offline transactions.
July 3, 1988: Initial Issuance of X.509
On July 3, 1988, X.509 was initially issued in association with the X.500 standard. It was created to provide users with secure access to information resources and prevent cryptographic man-in-the-middle attacks. The standard assumes a strict hierarchical system of certificate authorities (CAs) for issuing certificates, which contrasts with web of trust models like PGP.
1995: Formation of the Public-Key Infrastructure (X.509) Working Group
In 1995, the Internet Engineering Task Force (IETF), in conjunction with the National Institute of Standards and Technology, formed the Public-Key Infrastructure (X.509) working group, commonly referred to as "PKIX".
September 2002: PKI Forum Publication on Certification Path Construction
In September 2002, the PKI Forum published a document titled "Understanding Certification Path Construction". This document outlines a method for a Certificate Authority (CA) to transition from an old signing key pair to a new one by issuing certificates containing the old public key signed by the new private key and vice versa.
2004: Limited usage of X.509 version 3 in web of trust models
As of 2004, version 3 of X.509 had the flexibility to support topologies like bridges and meshes and it could be used in a peer-to-peer web of trust, similar to OpenPGP. However, it was rarely implemented in that way.
2011: CA/Browser Forum Requires Serial Number Entropy
Since 2011, the CA/Browser Forum has required serial number entropy in its Baseline Requirements Section 7.1 to mitigate the risk of hash collision exploitation in X.509 signatures. This requirement helps prevent attackers from predicting the data that the certificate authority will sign by including a random component in the certificates.
June 2014: Conclusion of the Public-Key Infrastructure (X.509) Working Group
In June 2014, the Internet Engineering Task Force's Public-Key Infrastructure (X.509) working group, known as "PKIX", concluded its work after producing RFCs and other standards documentation on using and deploying X.509 in practice.
2014: PKI Forum Document Retrieved
In 2014, the PKI Forum's "Understanding Certification Path Construction" document from September 2002 was retrieved.
January 1, 2016: Baseline Requirements Forbid Issuance of SHA-1 Certificates
As of January 1, 2016, the Baseline Requirements forbid the issuance of certificates using SHA-1.
May 2017: Edge and Safari Reject SHA-1 Certificates
As of May 2017, both Edge and Safari browsers began rejecting certificates that use SHA-1.
2019: Browsers Begin Hiding EV Certificate Indicators
In 2019, major browsers like Chromium and Firefox began hiding the extended validation (EV) issued-to information in sub-menus. This change was made due to studies and reports indicating the ineffectiveness of EV certificates and their potential for misuse by criminals to inject misleading elements into the browser's UI. Prior to 2019, browsers provided strong visual feedback for sites with EV certificates.
2019: PKI Forum Document Archived
In 2019, the PKI Forum's "Understanding Certification Path Construction" document from September 2002 was archived.
September 2021: OpenSSL Rejects SHA-1 Certificates by Default
In September 2021, OpenSSL began rejecting SHA-1 certificates by default in version 3.0.
Mentioned in this timeline

Microsoft an American multinational technology corporation headquartered in Redmond Washington...

September is the ninth month of the year in the...

A safari is an overland expedition most notably in East...
The letter S or s is the th letter in...
Software comprises computer programs that provide instructions for a computer...
Trending
52 minutes ago Illinois defeats Houston, advancing to Elite Eight in NCAA Tournament Sweet Sixteen.
The Kings Sharks rivalry is an NHL rivalry between the Los Angeles Kings and San Jose Sharks fueled by their...
53 minutes ago Phillies Opening Day: New Options, History, and a Gamble with Nature Unfolds.
53 minutes ago Brandon Miller Scores 21 Points, Applauded Crowd, and Throws a Poster Slam.

2 hours ago Robert De Niro passionately calls for Trump's removal at 'No Kings' rally.
2 hours ago Iranian Strike Injures US Troops in Saudi Arabia; Middle East Tensions Rise.
Popular

Sir David Attenborough is a highly influential British broadcaster biologist...
Kelsey Grammer is a celebrated American actor best known for...

William Franklin Graham III commonly known as Franklin Graham is...
Chuck Schumer is the senior U S Senator from New...
XXXTentacion born Jahseh Dwayne Ricardo Onfroy was a controversial yet...
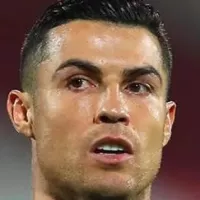
Cristiano Ronaldo known as CR is a Portuguese professional footballer...